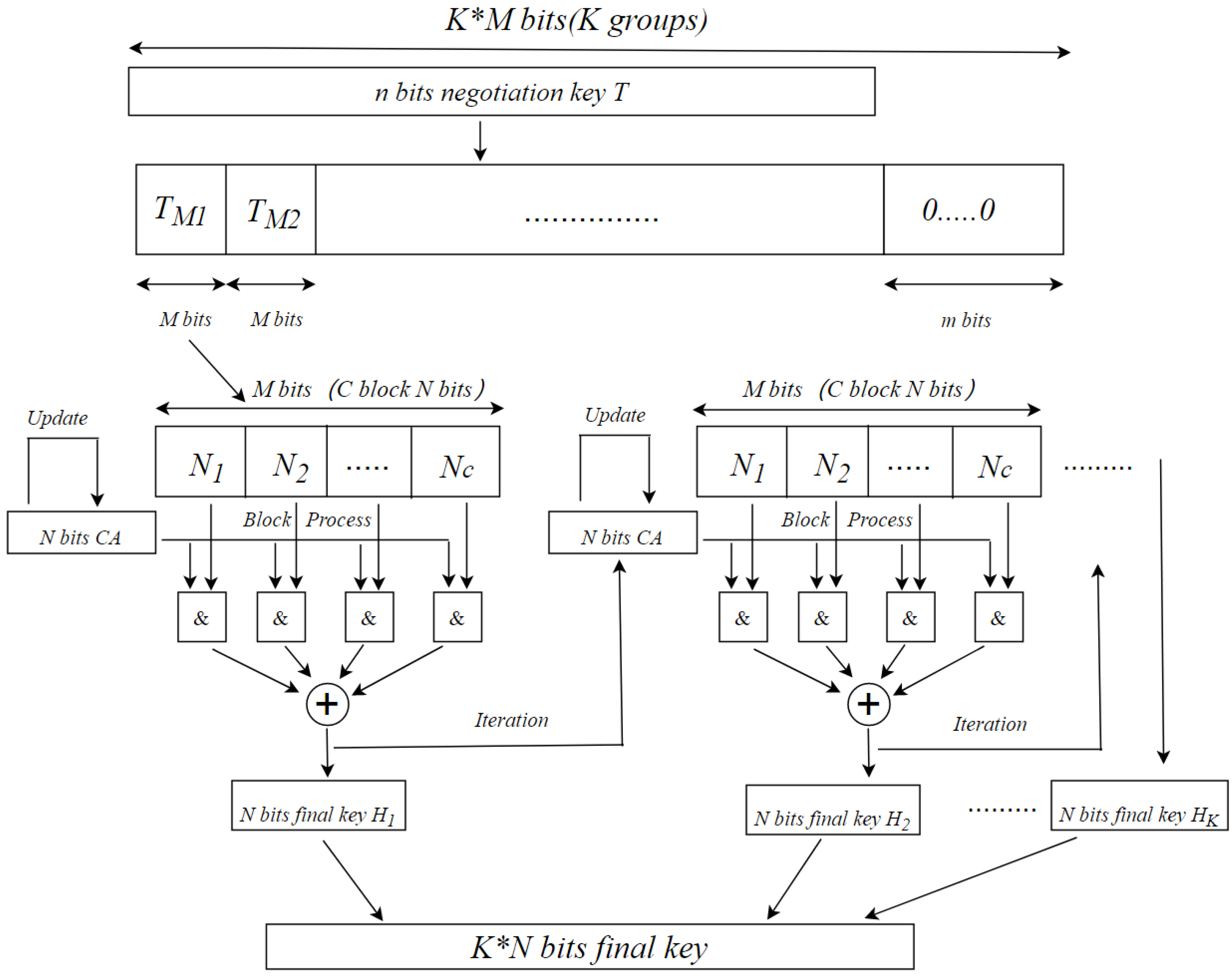
High-speed and Large-scale Privacy Amplification Scheme for Quantum Key Distribution | Scientific Reports

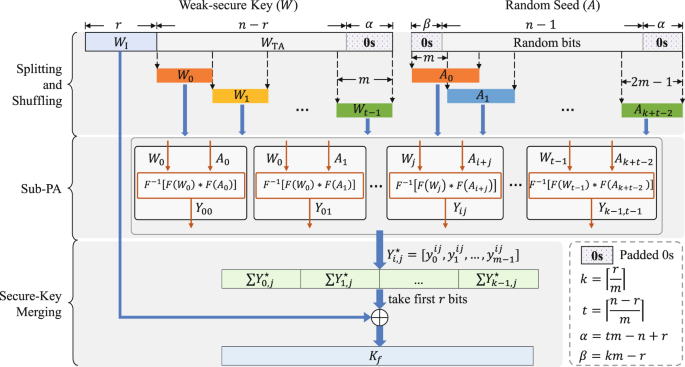
Analysis of the information theoretically secret key agreement by public discussion - Wang - 2015 - Security and Communication Networks - Wiley Online Library
![PDF] High-Speed and Adaptive FPGA-Based Privacy Amplification in Quantum Key Distribution | Semantic Scholar PDF] High-Speed and Adaptive FPGA-Based Privacy Amplification in Quantum Key Distribution | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/2a6df792aeac6ed6d0db5e99a269b7a34746fa7b/2-Figure1-1.png)
PDF] High-Speed and Adaptive FPGA-Based Privacy Amplification in Quantum Key Distribution | Semantic Scholar
Pre-Privacy Amplification: A Post-Processing Technique for Quantum Key Distribution with Application to the Simplified Trusted Relay

The process of length-compatible privacy amplification algorithm. The... | Download Scientific Diagram

Privacy Amplification with Couplings and Overlapping Mixtures | Rafik Hariri Institute for Computing and Computational Science & Engineering
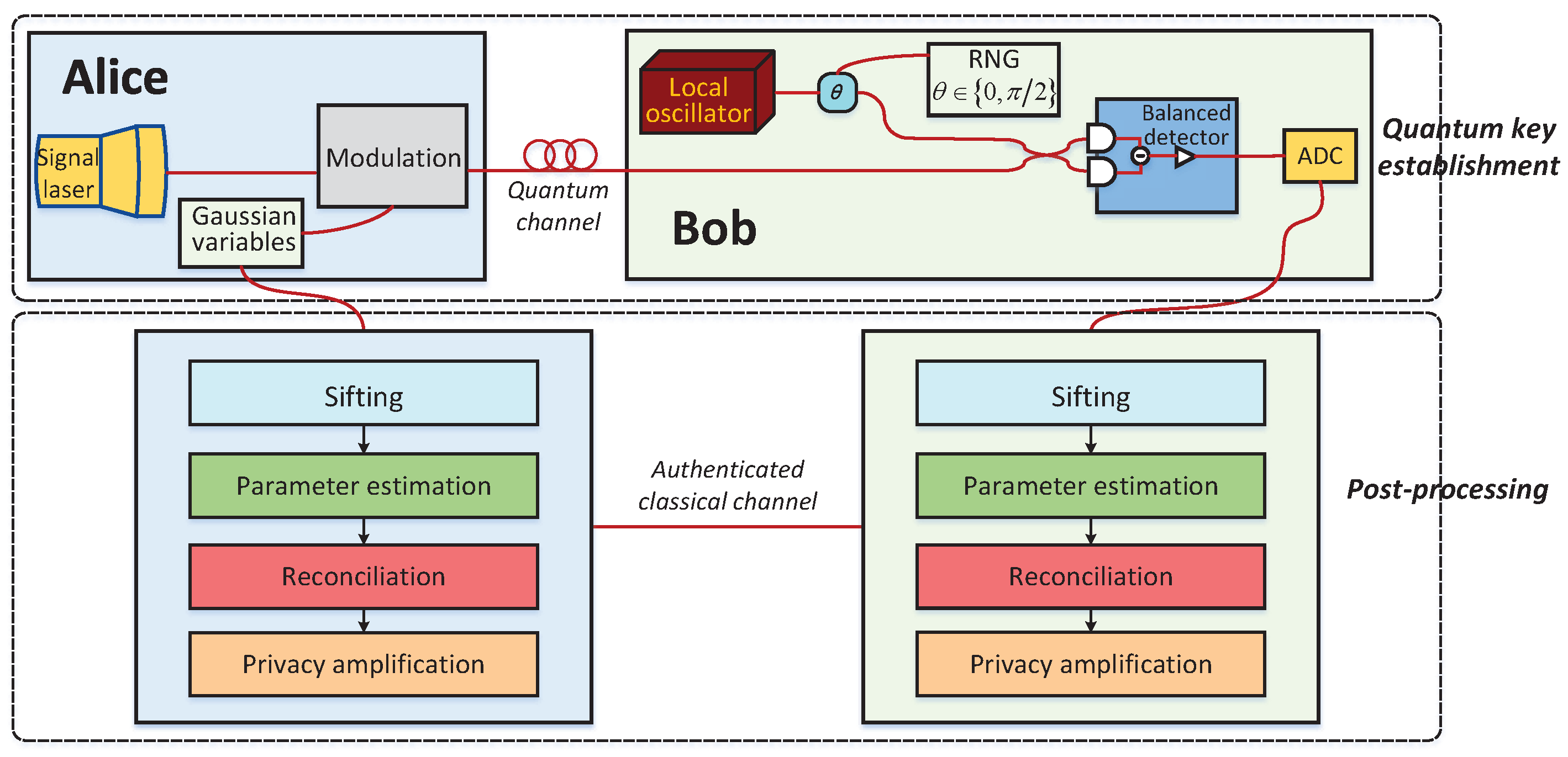
Entropy | Free Full-Text | An Improved Slice Reconciliation Protocol for Continuous-Variable Quantum Key Distribution
Underline | Echo of Neighbors: Privacy Amplification for Personalized Private Federated Learning with Shuffle Model